The appearance of a British national in a Westminster courtroom on charges of membership in al Shabaab represents more than a localized criminal proceeding; it is a data point in the shifting logistics of non-state militant organizations. While traditional news cycles focus on the spectacle of the arrest, an analytical deconstruction reveals a sophisticated supply chain of ideology and personnel that bypasses conventional border security through digital and social engineering. This case serves as a primary study in the Transnational Mobilization Framework, where the distance between a London suburb and a training camp in Somalia is bridged not by geography, but by a structured three-stage radicalization pipeline.
The Structural Anatomy of Membership Charges
To understand the legal gravity of "membership" under the Terrorism Act, one must parse the distinction between ideological affinity and operational integration. The British judicial system operates on a binary of proscribed participation. When a suspect is charged with being a member of al Shabaab, the prosecution is not arguing a matter of opinion, but a matter of functional alignment with an organization’s hierarchy.
The evidentiary threshold for such a charge generally requires proof of one of three operational signatures:
- Formal Oath of Allegiance (Bay'ah): A verifiable commitment to the group’s leadership structure.
- Logistical Contribution: The provision of technical skills, financial conduits, or recruitment services that directly enhance the group's lethality or sustainability.
- Command and Control Integration: Evidence that the individual has accepted instructions or training from the organization’s recognized officers.
The friction in these cases often lies in the "grey zone" of digital support. Is a man sharing propaganda a member or a sympathizer? The legal pivot occurs when that individual moves from consuming content to facilitating the group’s objectives, effectively becoming a remote asset in the organization's broader tactical array.
The Cost Function of Al Shabaab Recruitment in the West
Al Shabaab’s recruitment strategy in the United Kingdom and Europe follows a clear Economic Utility Model. For the organization, recruiting a Western citizen involves high risk but yields a disproportionately high return on investment (ROI).
- The Intelligence Premium: Western recruits possess cultural fluencies and linguistic capabilities that indigenous fighters lack. This allows for more effective digital propaganda tailored to a global audience.
- The Ease of Transit: A British passport is a high-value asset in the global logistics of militancy. It permits movement through international hubs with a lower scrutiny profile than passports from high-conflict zones.
- The Psychological Signal: Success in recruiting from the "enemy's heartland" serves as a powerful validation tool for the organization’s brand, assisting in local recruitment efforts within East Africa by projecting an image of global reach.
The internal mechanism of this recruitment relies on a "Sunk Cost" psychological bridge. Recruits are often encouraged to burn bridges with their past lives—financial, social, and legal—before they ever set foot in a conflict zone. By the time an individual appears in a courtroom in London, they have usually undergone a systematic shedding of their domestic identity, replaced by a rigid, functional role within the militant hierarchy.
Jurisdictional Mechanics and the Burden of Proof
The prosecution of returning or "homegrown" militants faces a recurring bottleneck: the Transnational Evidence Gap. Crimes allegedly committed in the semi-governed spaces of Somalia are notoriously difficult to prove in a London court. This creates a reliance on digital forensics and signals intelligence (SIGINT).
The evidentiary stack typically involves:
- Encrypted Communication Metadata: While the content of messages may remain obscured, the frequency, timing, and destination of pings to known al Shabaab IP addresses create a pattern of life consistent with membership.
- Financial Forensic Mapping: The movement of small, non-reportable sums through informal value transfer systems (Hawala) or cryptocurrency tumblers to known front organizations.
- Digital Footprints: Metadata from images or videos that place the individual in specific geographic locations associated with training activities.
This creates a tactical dilemma for the defense. If the prosecution can demonstrate a pattern of behavior that serves no rational purpose other than the advancement of a proscribed organization's goals, the "membership" charge becomes statistically difficult to refute.
The Three Pillars of Modern Radicalization Pipelines
Analyzing the trajectory of individuals charged with such offenses reveals a consistent structural process. It is rarely a sudden leap; it is a deliberate, staged transition.
1. Intellectual Decoupling
The individual is exposed to narratives that delegitimize their home state. This stage focuses on creating a "crisis of belonging," where the recruit's primary identity is shifted toward a globalized, militant interpretation of their faith.
2. The Social Echo Chamber
Radicalization is rarely a solitary act. It requires a peer group—often virtual—that reinforces the new identity. This group acts as a filter, removing dissenting information and accelerating the normalization of extremist violence.
3. Tactical Activation
The final stage involves a transition from theory to practice. This is the "Point of No Return" where the recruit seeks out facilitators to arrange travel or provides material support. At this stage, the individual moves from a security risk to a criminal target.
Geopolitical Implications of the Al Shabaab Network
Al Shabaab’s persistence as an al-Qaeda affiliate is rooted in its ability to maintain a dual-threat capability: a localized insurgency in Somalia and a globalized ideological franchise. The appearance of a British national in court is a symptom of this second capability.
The organization operates with a decentralized command structure that allows for "autonomous cells" to function in the West. These cells do not require direct, daily oversight from the leadership in Somalia. Instead, they operate on a Mission Command philosophy, where the objective is clear (recruitment, funding, or disruption), but the methods are left to the discretion of the local operative.
This creates a significant challenge for British intelligence services (MI5 and Counter Terrorism Policing). Monitoring every individual with radical sympathies is a resource-intensive task with diminishing returns. The focus, therefore, shifts to identifying the "Gatekeepers"—the high-value individuals who possess the specific connections to facilitate the transit of recruits or the laundering of funds.
Technical Limitations of Counter-Terrorism Strategies
Despite the rigor of the judicial process, several systemic vulnerabilities remain. The use of end-to-end encryption (E2EE) has created a "Going Dark" problem for investigators. When communication occurs within silos that even the platform providers cannot access, the ability to preemptively disrupt a cell is significantly reduced.
Furthermore, the legal definition of "terrorism" continues to evolve. As militant groups adopt more fluid, decentralized structures, the traditional legal frameworks designed for 20th-century insurgencies are being tested. The current case highlights the necessity of a Multi-Vector Attribution approach, where guilt is established not through a single smoking gun, but through the convergence of digital, financial, and physical evidence.
The court proceedings will likely hinge on the "Specific Intent" of the defendant. Under English law, the prosecution must prove that the individual didn't just stumble into these associations, but intended to further the aims of al Shabaab. This requires a deep dive into the defendant’s digital history, seeking the specific moments where a clear choice was made to prioritize the organization over the state.
Strategic Trajectory of Domestic Threats
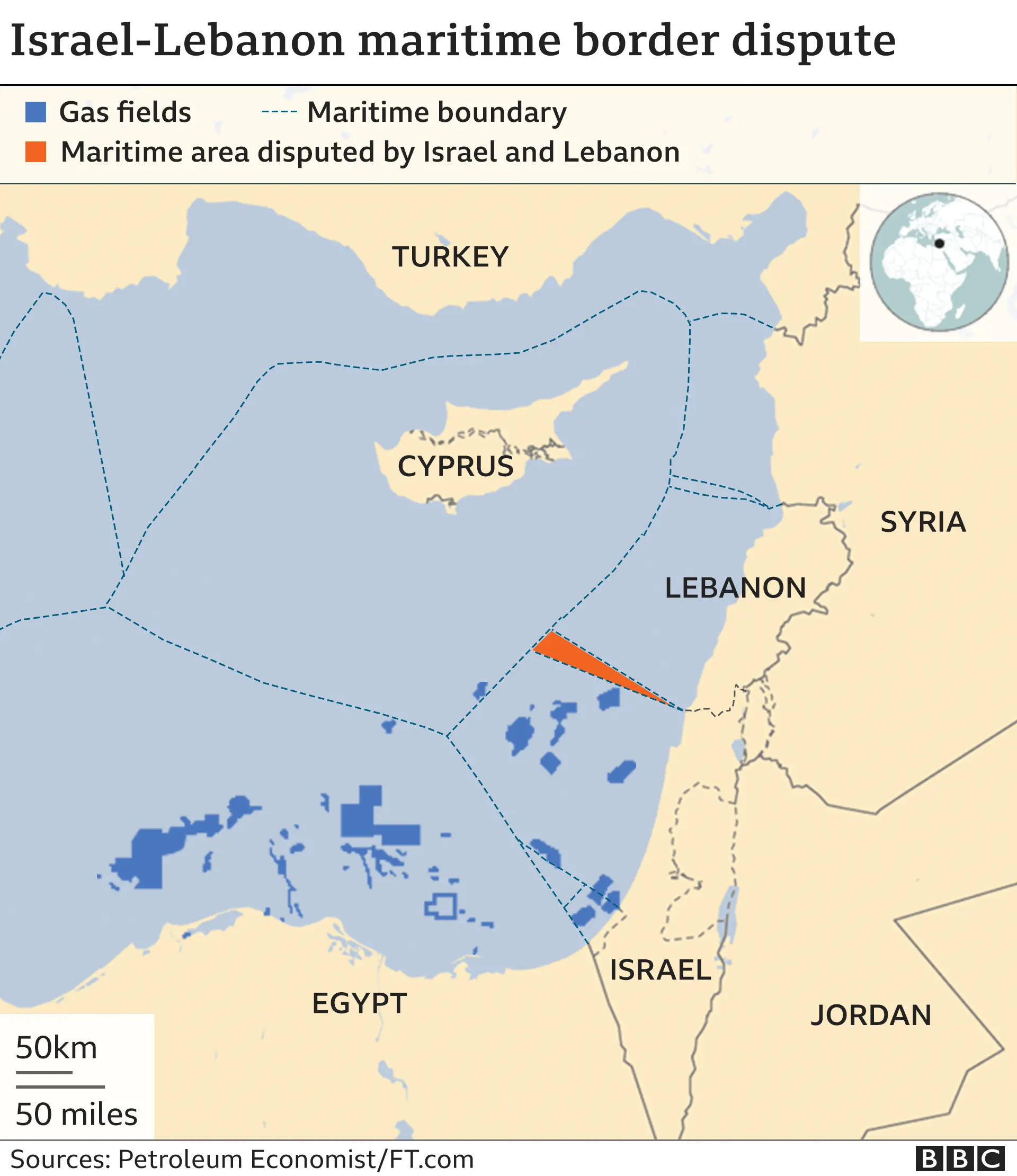
The arrest and charging of British nationals in connection with East African militancy indicate a shift in the "Threat Landscape." While the focus for the past decade was largely on the Levant (Syria and Iraq), the operational gravity is pulling back toward the Horn of Africa and the Sahel.
Security agencies must now account for a Circular Recruitment Loop. Recruits from the West provide the technical and financial support that allows the organization to survive local military pressure; in turn, the organization’s survival provides the "glory" and "purpose" that attracts the next wave of Western recruits. Breaking this loop requires more than individual arrests; it requires the systematic degradation of the digital infrastructure that hosts these recruitment pipelines.
The prosecution of this case will serve as a bellwether for how the UK handles the next generation of transnational militants. It signals a move toward high-granularity digital investigations and a lower tolerance for "passive" involvement in proscribed groups.
The strategic priority for counter-terrorism analysts is now the identification of the "Logistical Nodes"—the individuals who may never pick up a weapon but who provide the administrative and digital scaffolding upon which organizations like al Shabaab depend. Disruption of these nodes offers a higher systemic impact than the arrest of a single foot soldier. The focus must remain on the Infrastructural Decay of the organization’s recruitment capability, targeting the technical facilitators who bridge the gap between radical thought and militant action.